Staging the Network
NOTE: I am assuming you have an existing Proxmox homelab set up, with two virtual switches ie. vmbr0 and vmbr1 (for the subnets). If you do not, please refer to my previous write-ups which describe installing Proxmox, pfSense and configuring the network.
We will be creating a new subnet in our pfSense firewall with the following attributes:
- VLAN ID Number: 80
- VLAN Network ID: 10.80.80.1/24
- Interface Name: AD_LAB
- DO NOT ENABLE the DHCP server on this VLAN, as the Domain Controller is going to be filling that role
General Steps
- Add a new VLAN to VMBR1 in Proxmox
- Add the VLAN to pfSense
- Configure the interface in pfSense
- Add firewall rules
Add a new VLAN to VMBR1 in Proxmox
Go to your Proxmox node > Network
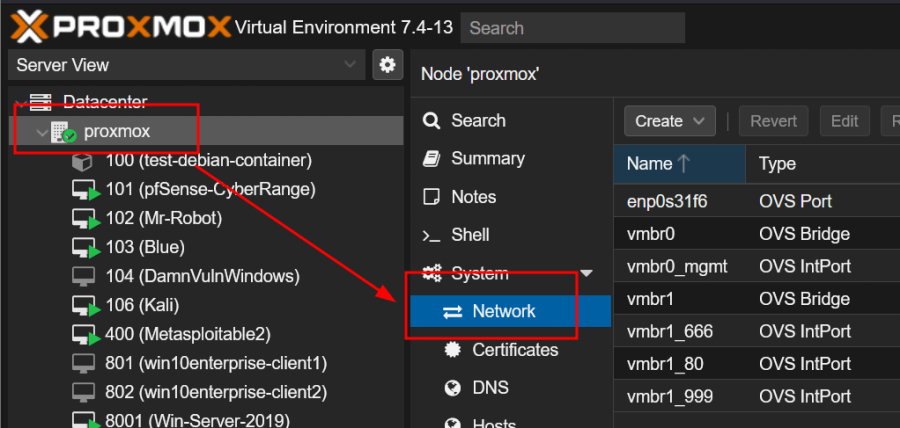
Select vmbr1 and click Create > OVS IntPort
- Fill out the fields
- When we attach a container or VM to the (internal) switch vmbr1 and tag it with the VLAN ID of 80, pfSense will route it through the intended VLAN
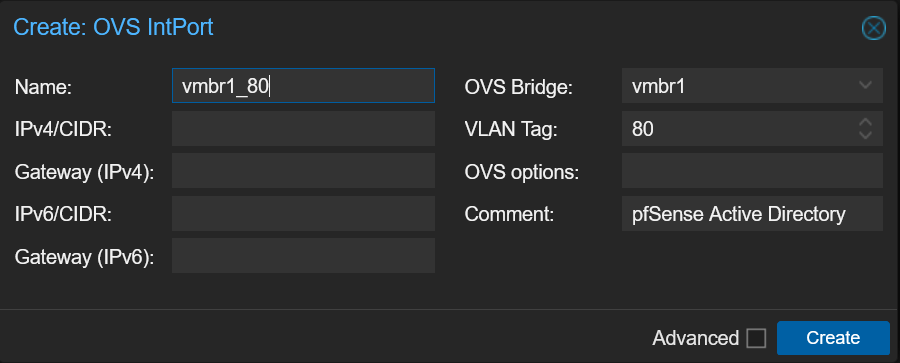
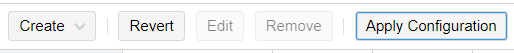
Be sure to click Apply Configuration
Add the VLAN to pfSense
In pfSense, add a new VLAN:
- Interfaces > Assignments
- Click on VLANs > Add
- Screenshot already has VLAN 80 added
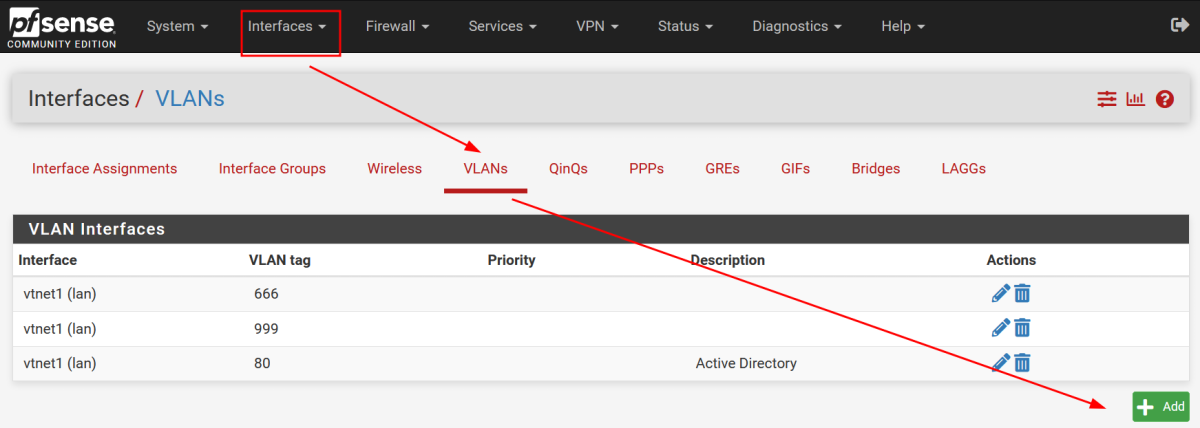
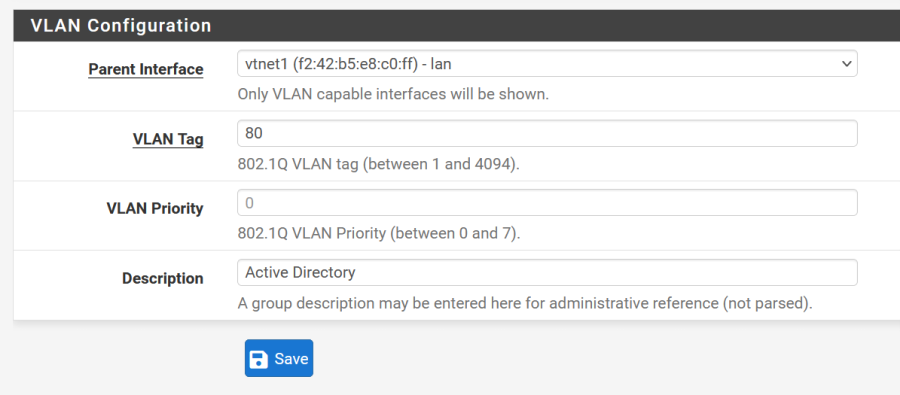
Enter these values:
- Parent Interface: vtnet1 (internal LAN interface)
- VLAN Tag: 80 (subnet/sub-interface of vtnet1)
- VLAN Priority: 0
- Description Active Directory
Go to Interface Assignments
- click Add next to the newly added sub-interface
Click Save
You should now see an OPT# interface - click on the OPT# interface name, to configure the interface.
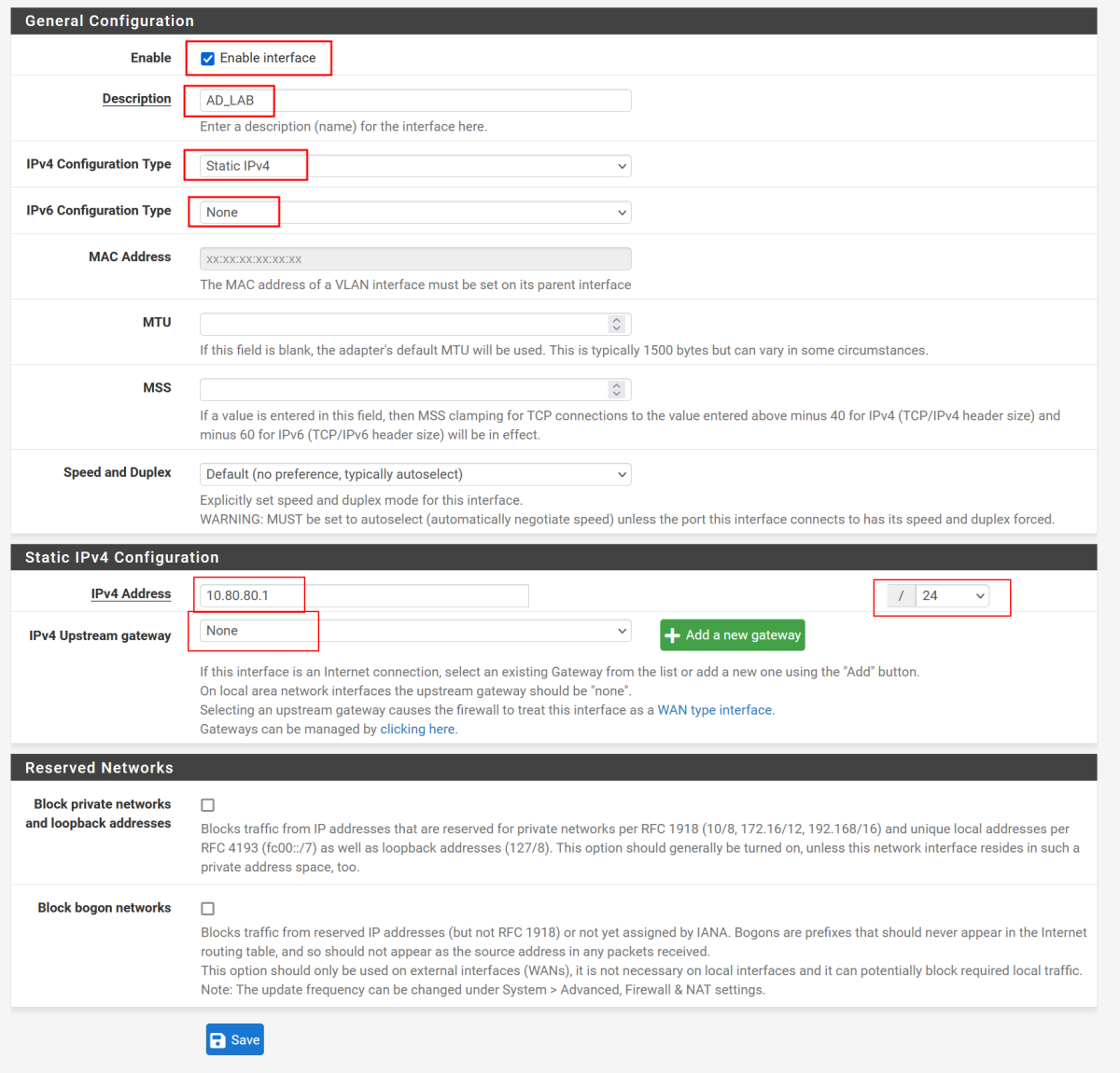
Configure the Interface
- Enable Interface
- Description: AD_LAB
- IPv4 Configuration Type: Static IPv4
- IPv6 Configuration Type: None
- IPv4 Address: 10.80.80.1 - /24
- IPv4 Upstream gateway: None
- Block bogon networks: Some suggest to enable this, I did not
Click Save and Apply Changes
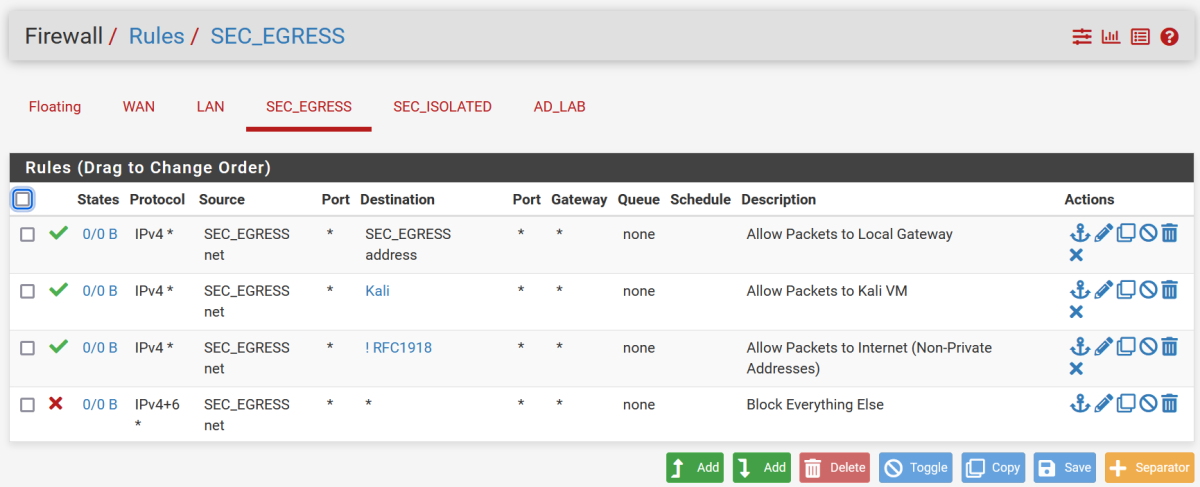
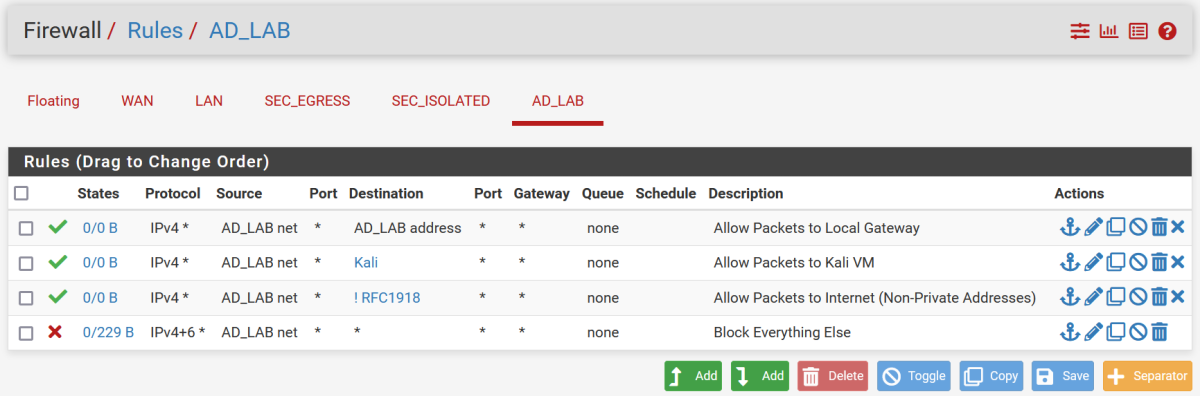
Add Firewall Rules
NOTE: The firewall rules are different than the rules used for the AD_LAB in our VMware/VirtualBox environment; the Proxmox subnet uses more sophisticated firewall rules to block private addresses. Private addresse were not blocked in our VMware environment.
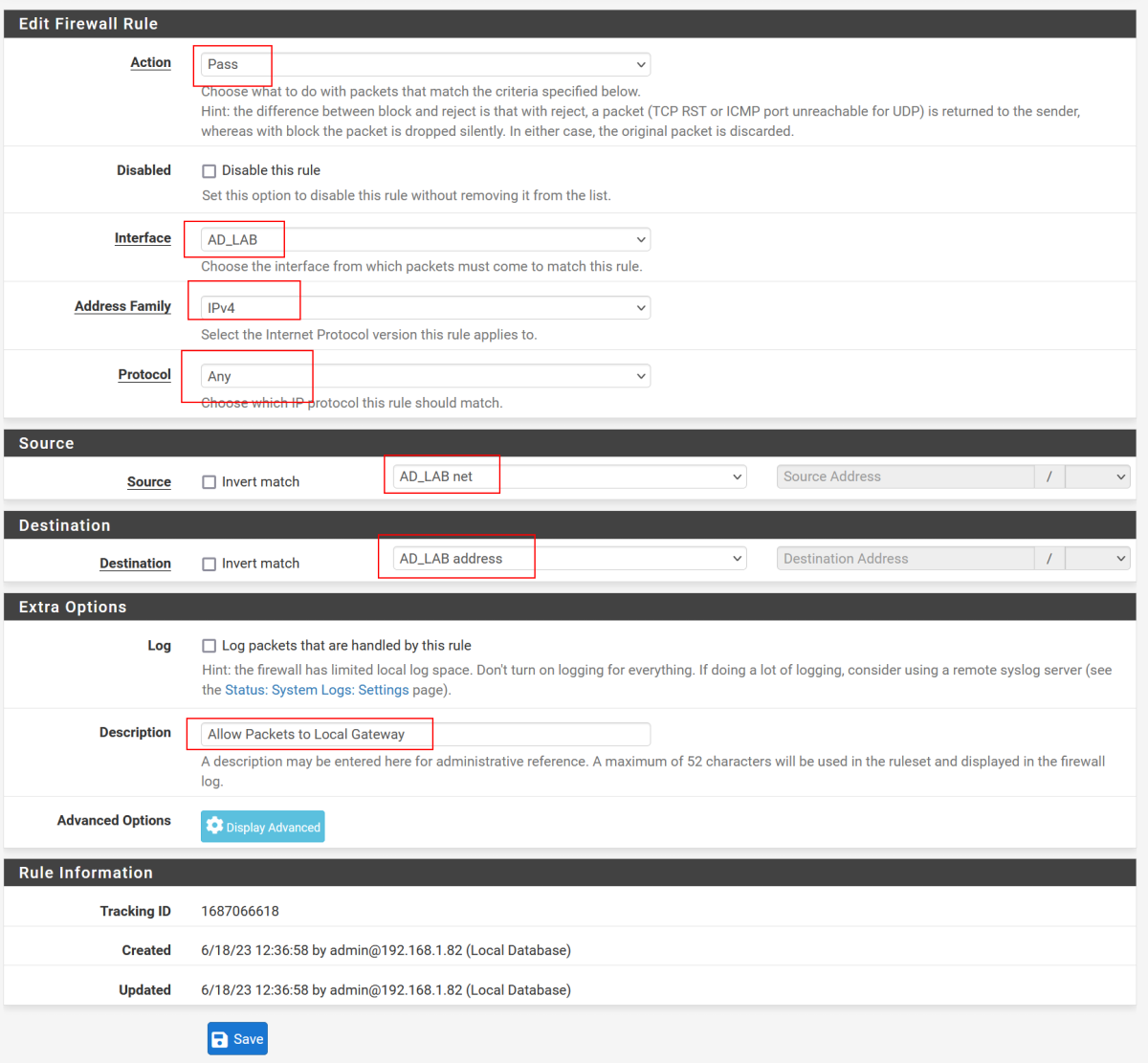
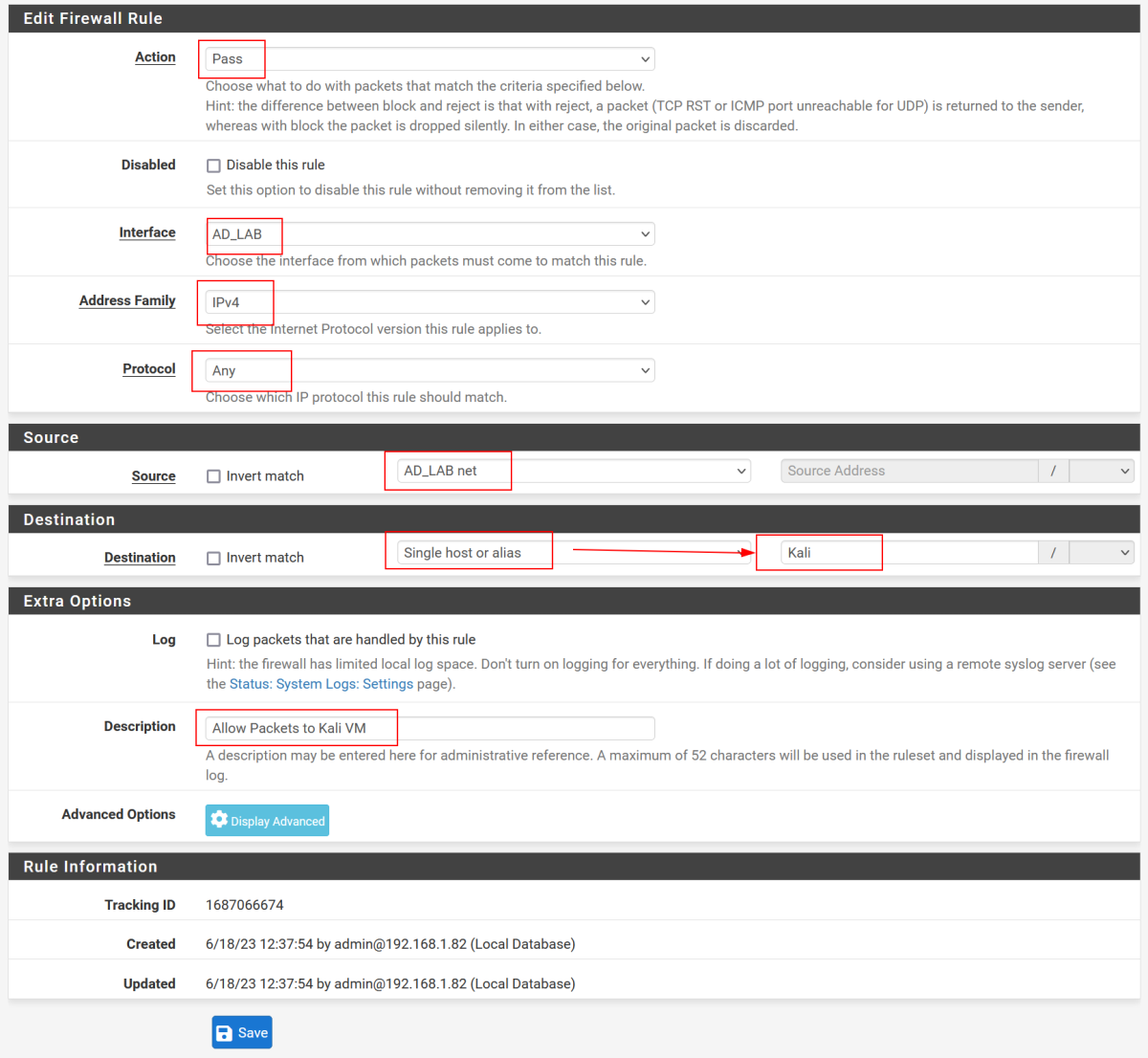
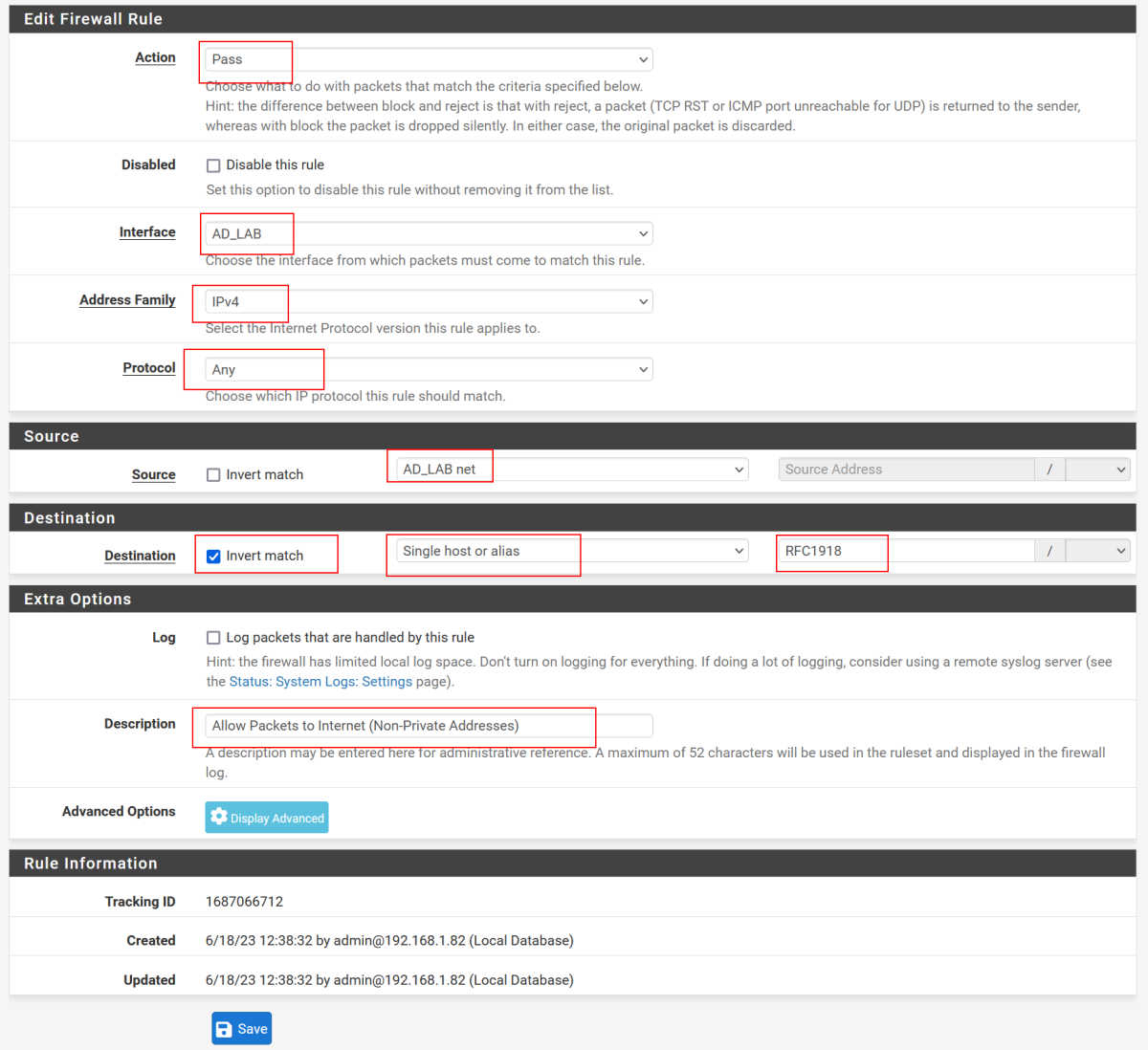
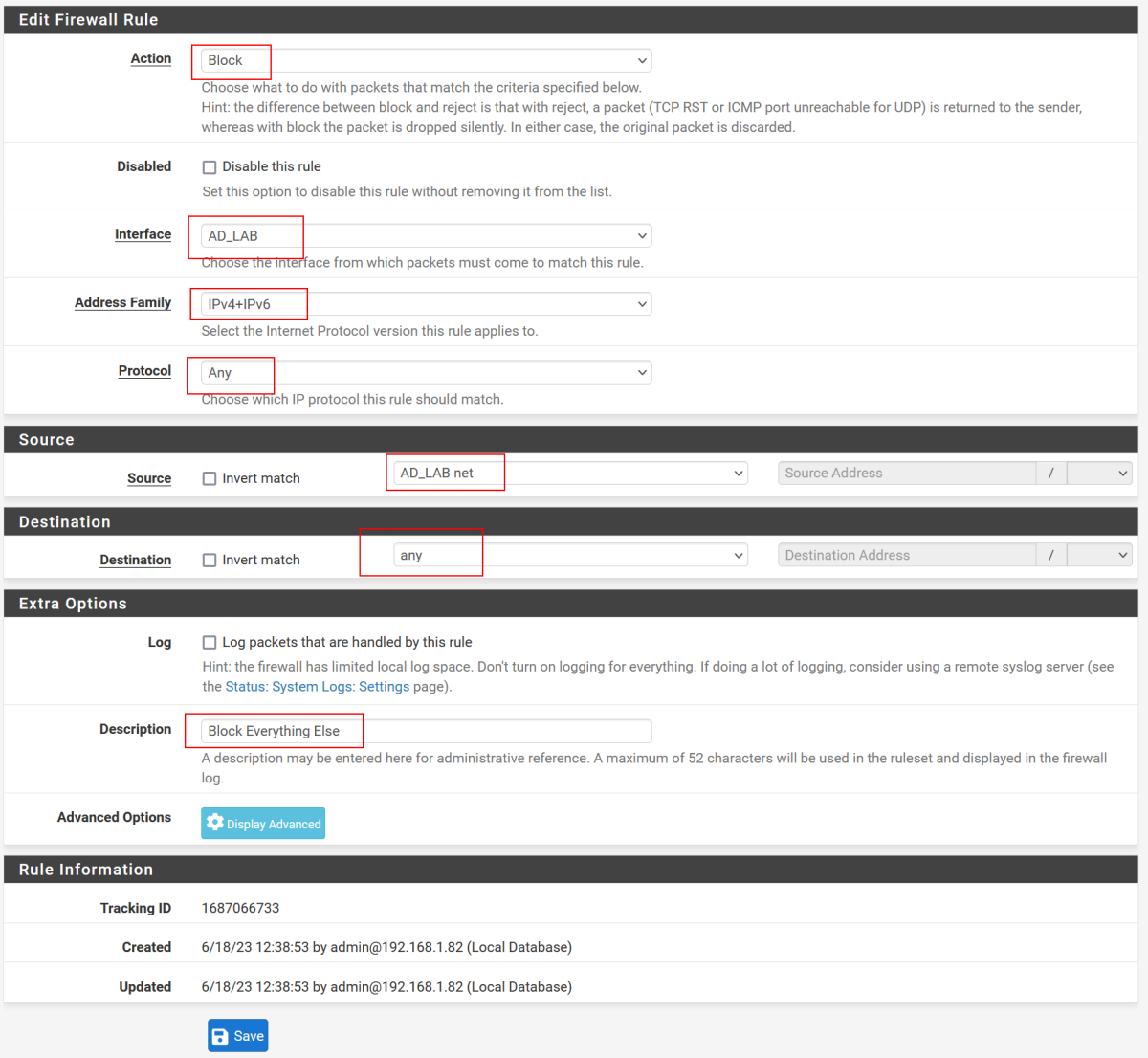
I copied the firewall rules used for SEC_EGRESS (see previous pfSense writeup) for AD_LAB - with the following rules:
- Allow Packets to Local Gateway: Packets need to be able to reach the default gateway in order to reach the internet. We did not have this rule in our VMware environment because we will be blocking RFC1918 (private network) addresses here
- Allow Packets to Kali VM: However, for some attacks to function properly, the attack box should be on the same subnet as the Active Directory Forest
- Allow Packets to Internet (Non-Private Addresses): Note, this is an Invert Match
- Block Everything Else
Allow Packets to Local Gateway
Allow Packets to Kali VM
Allow Packets to Internet (Non-Private Addresses)
- NOTE: Invert Match. We had previously defined RFC1918 as Private Internet Addresses. So we are allowing traffic to non-RFC1918 addresses.
Block Everything Else
This is the desired end state for SEC_EGRESS and AD_LAB: