Warning & Preamble
This is my most ambitious blog project to date and spans a series of 9 posts. Instead of one very long post, I have separated the major sections into their own post; I did this primarily for my own reference if I need to refer to a particular stage in the process. This might be easier to find then scrolling through a long article.
I owe much gratitude to Heath Adams aka TheCyberMentor and his amazing academy for helping me begin and sustain my cybersecurity journey over the past 3 years. It was an honour to meet him in person at DefCon 31 this past summer. I am also indebted to Ben Heater, whose blog posts helped me create my first VMware homelab in 2022, and then introduced me to the power of Proxmox in 2023. I hope to be able to meet him in person one day.
Introduction
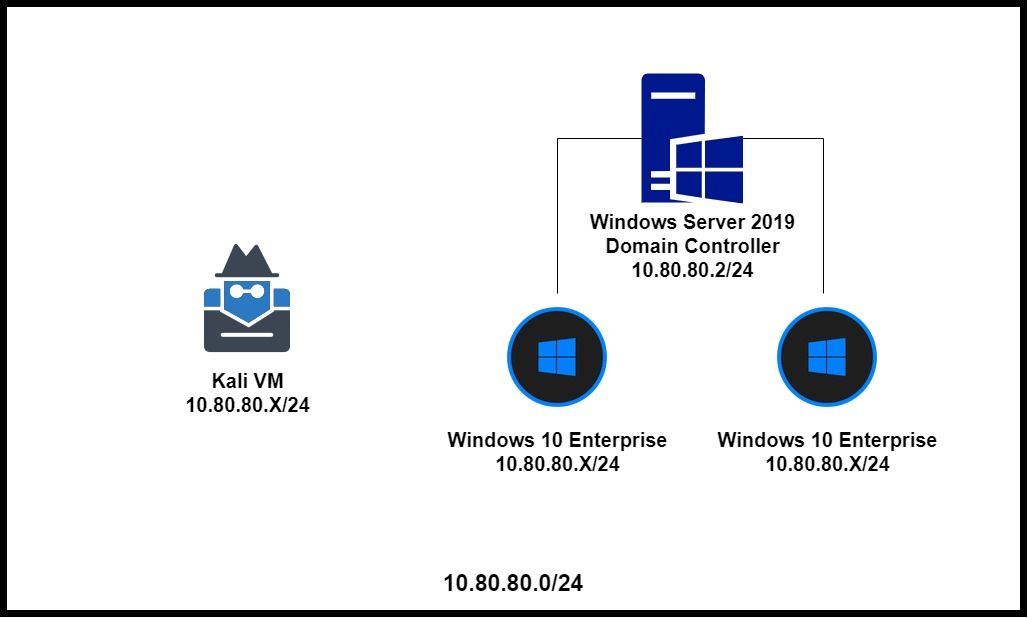
My goal is to summarize the steps necessary to create a small Active Directory (AD) forest (including a Domain Controller [DC] and two Winows 10 Enterprise clients). This AD Lab can then be used for educational purposes, and to practice vulnerability and feature assessment techniques.
This document is a mash-up of Ben Heater’s excellent guide(s) to creating an AD forest in Proxmox, as well as instructions from Heath Adams to replicate the AD forest used in The Cyber Mentor’s (TCM) Practical Ethical Hacking course. The Active Directory section is second to none, and has disrupted the cybersecurity educational industry, resulting in some established academies to update their course materials. My intention is not to plagiarize content from other sources, but amalgamate them into one place, primarily for my own reference; however, I will be very pleased if you or others find it useful too.
Content for my project are based on these invaluable sources:
- https://benheater.com/proxmox-lab-windows-guest-best-practices/
- https://benheater.com/proxmox-lab-active-directory-lab/
- https://academy.tcm-sec.com/p/practical-ethical-hacking-the-complete-course
Main Sections
I have broken up the process into these 9 sections. They all reside in my HOMELAB PROXMOX section:
The individual links are here:
- Windows Guests & Proxmox
- Obtaining the ISOs
- Staging the Network
- Adding/Removing Kali on AD VLAN
- Install and Configure Windows Server 2019/2022
- Install and Configure Windows 10 Enterprise Clients
- Setting Up Users, Groups, and Policies
- Joining Our Machines to the Domain
- Troubleshooting ie. Leases
NOTE: This AD Forest subnet is intentionally insecure
As Ben and others have noted elsewhere, the proper way to host an Active Directory forest is to have the domain controller (DC) on a separate subnet(s) from the Windows clients. However, for the purposes of our homelab, where the intention is to practice exploiting features and vulnerabilities, we will be intentionally creating a flat network. This will increase the probability of successful attacks, for the purposes of education and learning. This also includes having the Kali attack box on the same flat subnet (this will be covered in its own post).
This diagram is from https://benheater.com/content/images/2022/04/33066aafa8fc4acaaa6271f389191fa9.png